BlueID Ready2Go implementation
BlueID Ready2Go implementation
About
As many of our customers want to use similar chips, we decided to help our customer by providing a ready to use implementation of our security technology for selected Bluetooth LE System on Chips.
BlueID Ready 2 Go Implementation
To reduce the time to market of your new product, we provide Ready2Go implementations for selected hardware platforms. These implementations are provided as firmware images, that can directly be flashed onto the chip or module. Key features of Ready2Go implementations are:
-
Full integration with BlueID core developed by BlueID core developers.
-
Well tested code base which is maintained and steadily updated by BlueID core developers.
-
Reliable measurements on current consumption and other important key figures such as RAM and Flash consumption of manufacturer libraries and BlueID. Plan your project in advance!
-
Take advantage of BlueID GmbH's experience with other customer projects which includes in-depth knowledge of important device-specific features such as Over-the-Air (OTA) updates.
-
Easy to extend or replace functionality with your own sub-routines.
-
Avoid common security pitfalls by taking advantage of our peer-reviewed security modules in your own code.
-
Centralized configuration interface. With this you can flash new device parameters without compiling a new firmware.
-
Customization can be offered
Currently supported Ready2Go platforms
In the recent we have these platforms already integrated for you:
Your desired platform is not listed yet? Please give us a call. We expand our list of supported platforms steadily!
How to integrate
To integrate a R2G implementation, you have to do these things:
during development
-
select a BLE chip form our list of supported platforms.
-
put BLE chip into your schematics and wire it accordingly.
during production
-
flash Ready 2 Go firmware onto the selected BLE chip.
-
use BlueID initializer tool to generate individual init data for each device and flash it onto the chip (Initialization of secured objects)
-
ship product.
Advantage
BlueID integration without Ready2Go Firmware image
|
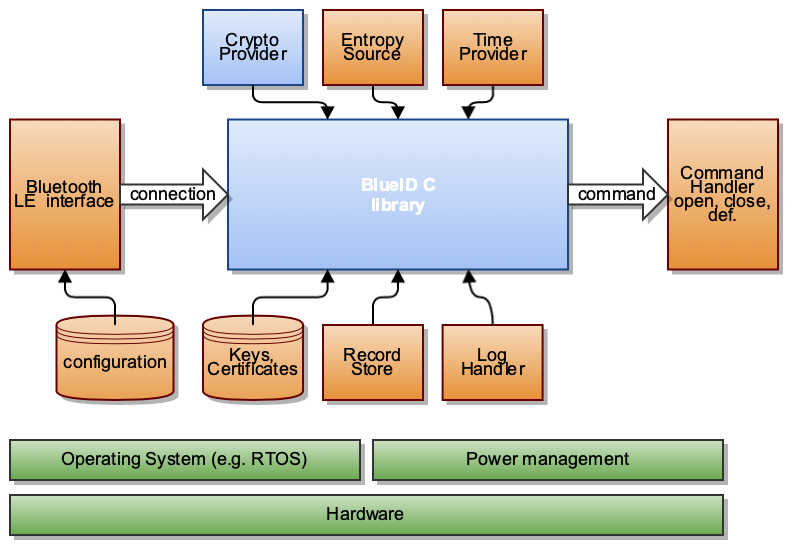
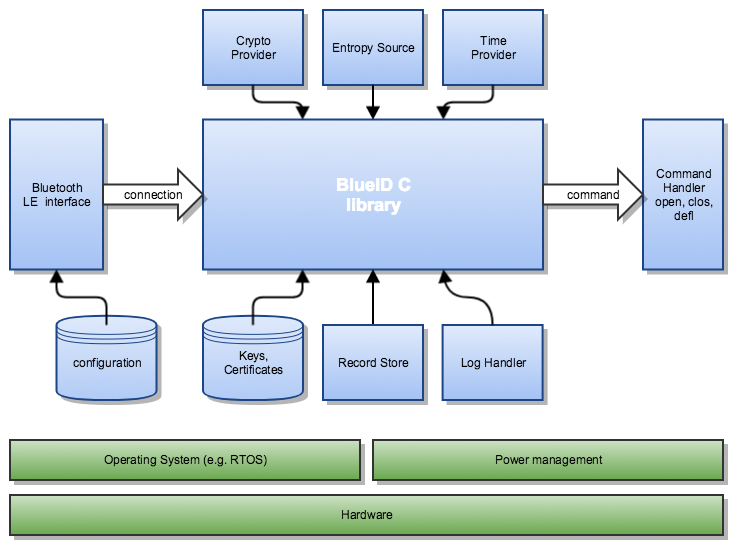
Within the BLE Chip, the "Blue" part is what BlueID provides as standard their standard SDK however the lock manufacturers need to prepare all the parts mentioned in "Orange". Developing these parts required resource allocation which eventually result in higher development cost and delay in market readiness.
BlueID integration with Ready2Go Firmware image
|
On the other hand, now as BlueID provides ready to use firmware image of BGM111, all the "Orange" part is already a part of the firmware image and the lock manufacturers save a lot of time and cost and their locks will become "smartphone ready" locks within a short time period.
Below is the list of all BlueID components integrated into the firmware image for BGM111:
| Components | Description |
|---|---|
| BlueID for C Core library | The BlueID SDK for C is integrated into the operating system and connected to all the components below |
| Crypto Provider | Included into BlueID the crypto provider is a module that provide the cryptographic algorithm. It brings flexibility on the choice of the algorithm and is optimized for the ARM Cortex architecture. |
| Bluetooth LE Interface | This service allows to receive and send data bi-directionally from and to the BlueID enabled smartphone. Therefore, the Bluetooth LE interface puts the BLE stack into advertising mode and waits for a smartphone to connect. The advertisement datagram consists only of the local name required by BlueID. The advertisement response datagram contains the BlueID UUID. The advertisement rate, the connection interval and the transmit power can get adjusted in the configuration of the Ready2Go implementation. Please note that the hardware starts to advertise after powering up the device until a connection comes in. After a connection has finished, the device starts to advertise again. |
| Configuration | The configuration contains data loaded during start up of the hardware. The configuration data is then used by the BLE interface to set the values for advertisement rate, the connection interval and the transmit power. |
| Entropy Source | BlueID requires a good source of entropy. The Ready2Go implementation contains an implementation of the entropy source stub. This implementation uses the best available source of entropy on the device. Usually this is a TRNG. |
| Time Provider | BlueID Tokens have a time restriction. Therefore, the BlueID Ready2Go implementation uses the internal clock of the hardware to provide a time source. This RTC can get set by the BlueID command time. |
| Record Store | The BlueID Ready2Go implementation provides a record store for revocations and for the BlueID incident log feature. This implementation persists data to either the internal flash or an internal EEPROM. See the platform details for more information |
| Log Handler | The log handler sends out the BlueID log data to a hardware platform specific debug port. This can be an UART or a RAM area automatically read by the hardware platform specific debugger. |
| Key and Certificate | The BlueID Ready2Go implementation provides a store for private key and certificate. This implementation persists data to either the internal flash or an internal EEPROM. See the platform details for more information. |
| Power management | The BlueID Ready2Go implementation optimizes the power consumption of the hardware. This optimization is done based on the following parameters:
For reaching an optimized power management, the BlueID Ready2Go implementation switches off all not required components of the hardware like UART, Timers, and GPIO. The remaining power consumption is usually reduced to the power required by the RTC, Deep Sleep Mode and mostly the advertising of the BLE subsystem. |
| Operating system | BlueID SDK for C is a software stack. To run it on a hardware platform, some form of an operating system is required. This can be a RTOS or a very simple event oriented hardware stack. BlueID GmbH decides, based on the provided hardware and its common tools, which type to use here. |
BlueID Standard Commands
BlueID Access Commands
| Command | Description | Electrical function |
|---|---|---|
| time | Set the time (in UTC) on the real-time clock | none |
| gtim | Retrieve the time of real-time clock as a UTC timestamp | none |
| gual | Retrieve a list of all authorized and unauthorized user accesses on the secured object | none |
| cual | This command clears the user access log | none |
| vers | Retrieve the version of the BlueID SDK on the secured object as a string | none |
BlueID Ready2Go Commands
| Command | Description | Electrical function | ||||
|---|---|---|---|---|---|---|
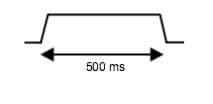
| tokn | Set the pin A for a configurable delay to high |
|
||||
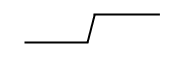
| enof | Activate the pin A (high level) |
|
||||
| diof | Deactivate the pin A (low level) |
|
||||
| tria | Toggle the output level of pin A |
|
||||
| opeb | Set pin B for a configurable delay to high |
|
||||
| ronb | Activate pin B (high level) |
|
||||
| rofb | Deactivate pin B (low level) |
|
||||
| trib | Toggle the output level of pin B |
|
||||
| deby | Activate the debug logging over UART | none | ||||
| debn | Deactivate the debug logging over USART | none |
Depending on hardware specification, feature may differ from this list.
BlueID features
BlueID Read2Go implements these extra features:
UART Logging
The BlueID Ready2Go firmware image provides the feature of logging the command execution's parameters on every command execution.
The data are transmitted on USART0 with 115200 bps. The serial port is configured with 8 bits, no parity bit, 1 stop bit and uses TTL levels (3.3V).
UART Logging can be activated and deactivated on run time.
The protocol for this data is described in Ready2Go UART protocol.
Power Profiles
For each BlueID Ready2Go implementation two profiles are available. They are tuned for different use cases.
Battery driven objects (low power optimized)
This configuration is optimized for saving battery life but still providing an outstanding reliabilty of the BLE command execution. Usually this is used for battery driven equipment like door handles and cylinders.
Externally powered objects
This configuration is optimized for fast connections from the smartphone to the lock resulting in faster opening. Usually this is used for powered objects like wall readers.
Key Figures provided for Ready2Go implementations
Key figures may vary based on applicability on the selected platform. Typically these key figures include:
-
Operating System like an RTOS
-
Listing of power consumption of different device operations
-
Type of device hardware peripherals being used
-
Maximum number of active record revocations
-
Maximum length of user access log
-
Flash endurance
-
Firmware program memory consumption
-
Max stack usage and static RAM usage
Software modules provided by Ready2Go
The following modules are part of every BlueID Ready2Go implementation. They are used by the BlueID core, but they are also available to your own code base.
-
Plug & Play experience for BlueID Bluetooth LE services
-
Implementation of BlueID commands (cp. chapter below)
-
Energy-optimized Real-Time-Clock (RTC)
-
Good random numbers from a well-tested entropy source maximizing security
-
Text logging facilities that eases your development
-
Fully functional record revocation and user access log modules which utilize the program flash memory as data storage. No need for external components.
-
Extensible configuration interface built for integration with BlueID's tool chain.